The Financial Data Access Regulation (FiDA) marks a fundamental shift in Europe’s financial ecosystem. It extends beyond open banking under PSD2 to a truly open finance framework, where customer consent enables sharing of data across banking, insurance, pensions, investments and other financial products. No longer are consumers and businesses limited to sharing information only from “payment accounts” (i.e., PSD2).
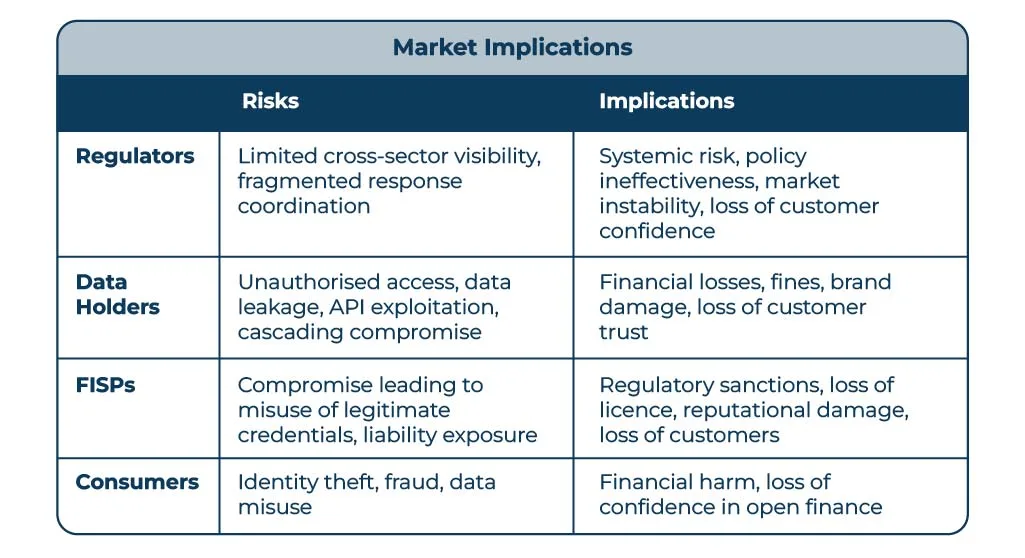
While this regulatory expansion fosters competition and innovation, it also widens the attack surface and introduces new systemic risks. FiDA participants, from data holders (banks, insurers, asset managers, etc.) to Financial Information Service Providers (FISPs) now operate within a complex trust fabric that spans borders, sectors and systems.
The evolving trust, security and cybersecurity threats in the FiDA ecosystem highlight the implications for regulators, financial institutions, FISPs and ultimately consumers & businesses, and the need to implement practical steps to ensure resilience, trust and consumer protection.
The transition from PSD2, PSD3 & PSR to FiDA represents an evolution from transactional data sharing (e.g. payment accounts) to holistic financial transparency. Under FiDA, individuals and businesses can permit accredited FISPs to access data held across financial verticals that include, but are not limited to:
- Retail and corporate banking accounts
- Credit and loan data
- Investment portfolios and pensions
- Insurance and risk data
This expansion significantly increases both the volume and sensitivity of data exchanged. While PSD2, PSD3 & PSR primarily focused on payments, FiDA touches nearly every aspect of a consumer’s financial life.
With more participants, including new entrants from non-banking sectors, comes fragmentation in governance, variable technical maturity and complex identity management. The result is a fragile trust layer where a single compromised participant could cascade risk across multiple data holders and jurisdictions.
While some threats may not yet be visible within the open finance ecosystem today, history has shown that complacency is costly. Over the past 12–24 months, multiple industries, from healthcare to critical infrastructure, have suffered severe compromises that began as unseen or underestimated risks.
The same trajectory could easily unfold in financial data sharing if emerging vulnerabilities are ignored. The absence of immediate incidents should not be mistaken for safety; rather, it is a window of opportunity to strengthen defences before adversaries exploit the inevitable weaknesses. To disregard these potential threats is not prudent.
With the lack of incident, security and data-exposure reporting under PSD2 in Europe, it is understandable that many financial institutions underestimate the security and operational risks posed by open banking and, by extension, FiDA.
This under-reporting is not solely a regulatory issue; it is also an operational one. In many institutions, open banking-related customer complaints, fraud queries, or data-access concerns raised through call centres and customer service channels are not classified as open banking incidents at all, but are instead logged under generic online banking, payments or data-privacy categories. As a result, open banking-specific risk signals are diluted, obscured or lost entirely within broader incident reporting frameworks.
The lack of meaningful incident reporting under PSD2 has been further compounded by fragmented supervisory interpretation, ambiguous definitions of what constitutes a “major” operational or security incident and overlapping notification obligations with the GDPR. Faced with uncertainty, many organisations have defaulted to GDPR breach notifications alone, rather than treating open banking incidents as distinct operational or security events requiring dedicated reporting and analysis.
Combined with reputational and commercial disincentives, immature monitoring capabilities, unclear responsibilities between banks and third-party providers and historically limited regulatory enforcement, this has resulted in under reporting. Cultural factors and the absence of feedback or shared incident data further exacerbate the problem. However, the recently implemented EU Digital Operational Resilience Act (DORA) aims to take steps to standardise incident classification, reporting timelines and aggregation, hopefully addressing some of these shortcomings.
This combination of regulatory ambiguity and internal misclassification has created a structural blind spot: institutions lack reliable data on the frequency, nature and impact of open banking incidents. In the absence of clear evidence, open banking is often perceived as low risk. That perception does not reflect reality; it reflects a failure of visibility. As PSD3/PSR and FiDA expand data access, increase ecosystem complexity and raise supervisory expectations, this historic under-reporting becomes increasingly untenable.
The FiDA Security Landscape
FiDA introduces a new generation of cyber and security risks that extend beyond those experienced under European open banking.
Every financial institution designated as a “data holder” under FiDA will be required to expose API endpoints that enable regulated and customer-consented Financial Information Service Providers (FISPs) to access client data. While this enhances data portability and competition, it will also substantially increase the number of publicly exposed APIs, thereby expanding the overall attack surface. Each endpoint represents a potential entry point for exploitation if not properly secured, continuously monitored and rigorously governed.
Data sharing will no longer be limited to access to transactional bank accounts. Under FiDA, the range of datasets that may be shared, subject to consumer consent, will expand significantly to include pensions, investments, credit products, loans, insurance and other financial services data. With the dramatic proliferation of data holders, the data sets that can/will be shared will become extremely attractive to fraudsters and criminals alike. The inclusion of insurance, investment and pension data introduces richer and more valuable personal and financial information, heightening the risks of fraud, identity theft and large-scale data misuse.
The risk is further compounded by the fact that customer data may also be accessed by entities that are not themselves regulated. These “fourth parties” are organisations that receive or process financial data from a regulated Third-Party Provider (TPP), such as an AISP or PISP, but are not authorised under PSD3 or FiDA by a national competent authority. Despite this, they may access, store, or analyse customer financial data. Examples include cloud service providers, analytics firms and subcontracted developers.
Neither PSD3, the PSR nor FiDA allow “shadow data flows” to escape regulation, but they rely heavily on regulated organisations to police their extended digital supply chains.
However, ignoring the role of fourth parties is no longer tenable: liability, reputation and systemic trust all flow upstream to the regulated institution.
As data sharing scales under FiDA, the weakest link may not be a financial institution or FISP, but the unregulated analytics vendor, cloud platform, or subcontractor sitting quietly behind them. As financial sectors converge, attackers can exploit compromised credentials or authorisations in one domain (e.g., payments) to pivot into others (e.g. investments or insurance), amplifying systemic risk across the ecosystem.
The Evolving Threat Landscape
FiDA’s expansion beyond banks, to include insurers, investment firms, pension providers and other non-bank financial institutions, introduces significant systemic risk as many of these new participants lack the security maturity, capital strength and supervisory experience of traditional banks. This creates uneven resilience across the ecosystem.
Weaker entities may use less robust cybersecurity controls, depend heavily on third-party providers and fall under fragmented regulatory oversight. The result is a broader attack surface where a breach in one area could compromise others, undermining consumer trust and threatening the integrity of the open finance framework. In essence, FiDA’s success will hinge on ensuring that every participant, not just financial institutions, meets consistent, high-grade security and operational resilience standards.
Decentralised oversight under FiDA (unlike PSD2, which benefits from a single EBA register and a relatively unified supervisory structure) spans multiple financial sectors, each governed by different regulators such as the EBA, ESMA, EIOPA and various national competent authorities. This fragmentation risks creating blind spots in supervision, delays in authorisation revocation and poor coordination during security or data incidents. Without a centralised view or harmonised oversight, there is a real danger that an unauthorised or compromised entity could remain active in one part of the ecosystem while being suspended in another, undermining both regulatory control and trust in the open finance framework.
FiDA enables real-time data sharing through open APIs, but trust and authorisation mechanisms must operate at equivalent speed. If a FISP is compromised, it may continue using valid credentials until revocation propagates across all data holders, creating a window in which attackers can exploit legitimate access. This underscores the need for real-time, synchronised revocation and trust management across the open finance ecosystem.
As FiDA expands data sharing across multiple financial data categories, consumers face growing complexity in managing consent, often unclear about who holds their data, for how long and for what specific purpose(s). This lack of transparency and control increases vulnerability to social engineering and consent phishing attacks, where malicious actors exploit user confusion to gain unauthorised access to financial information, undermining both consumer trust and the integrity of the open finance ecosystem.
FiDAs Evolving Trust Layer – The Need for a Trust Anchor
As FiDA expands the open-finance ecosystem beyond payment accounts to include a wide range of financial and non-financial data, the framework’s trust layer must evolve to manage a far more complex web of participants: financial institutions, FISPs, intermediaries etc. Ensuring that each party is legitimate, properly authorised and operating under valid credentials in real time becomes essential to maintaining systemic integrity and consumer confidence. Static registration lists or periodic certification are no longer sufficient in such a dynamic environment. Instead, FiDA requires a living, verifiable trust fabric, a continuously updated and accessible directory service, reflective of all the various regulatory databases and FiDA scheme membership details, constantly updated to provide a real time system that is reflective of the legal systems of record. This will enable instant verification of participant identity, authorisation status and trust level before any data exchange occurs.
This real-time trust anchor would function as the authoritative source of truth for all FiDA participants across the EU, integrating with eIDAS 2.0 digital identity frameworks and qualified trust services. By exposing secure APIs and machine-readable metadata, the directory would allow both human and automated systems to instantly confirm whether a participant is accredited, active and compliant. It would also support revocation and suspension events in near real time, mitigating fraud and unauthorised access. Beyond technical assurance, such a directory would foster transparency and interoperability allowing consumers, FiDA participants and regulators to rely on a single, trusted registry. In doing so, it would transform the FiDA trust layer from a static compliance requirement into a dynamic infrastructure of continuous verification and accountability.
Building Resilience and Trust
To secure the evolving open-finance ecosystem under FiDA, resilience and trust must be built through a layered defence strategy that combines strong technical, organisational, and ecosystem-wide controls. At the technical level, robust identity, PKI and directory services form the foundation of trust. A continuously updated directory of all FiDA participants serves as a live trust anchor, enabling instant verification, authorisation and revocation through secure APIs. These controls are reinforced by a Zero Trust architecture where every request is authenticated, authorised and monitored using fine-grained consent scopes and behavioural analytics. Continuous monitoring through centralised Security Information and Event Management (SIEM) and Security Orchestration, Automation and Response (SOAR) platforms, enhanced with User and Entity Behavioural Analytics (UEBA), ensures rapid detection and automated containment of anomalies or compromised participants. At the organisational and ecosystem levels, defence depends on mature governance and collaboration.
FiDA Metrics that Underpin Trust & Confidence
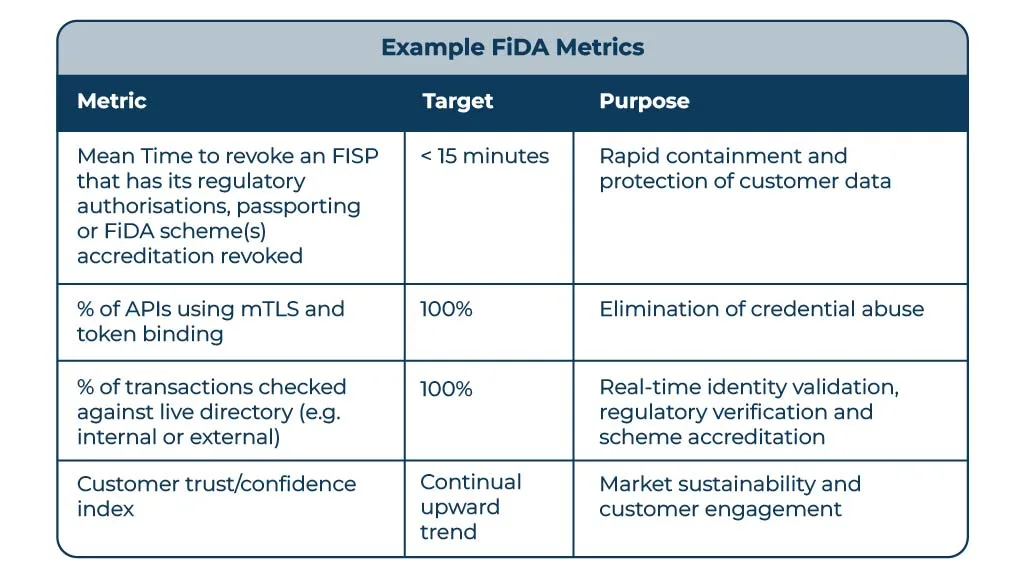
FiDA participants should monitor demonstrable, measurable outcomes to understand the effectiveness of their security, compliance and operational resilience controls, ensuring that trust and interoperability within the ecosystem are continuously validated.
Tracking metrics such as incident detection time, consent revocation speed, service uptime, authentication success rates and anomaly resolution time allow participants to quantify performance and identify weaknesses before they impact consumers or other ecosystem members.
These measurable outcomes provide the evidence that regulators, ecosystem participants and customers need to confirm that each participating organisation not only complies with FiDA’s technical and governance standards but also contributes to a secure, reliable and trustworthy data-sharing environment.
Failing to implement appropriate security and resilience measures exposes financial institutions to a compounding set of risks spanning cybersecurity, regulatory compliance and operational continuity. Technically, weak identity controls and lack of mutual TLS or token-binding open pathways for credential replay, lead to API exploitation and data exfiltration.
Gaps in directory services and certificate revocation checks can allow fraudulent or revoked participants to gain access, while supply-chain attacks targeting weaker FISPs can quickly spread across multiple institutions. These vulnerabilities not only create immediate exposure but also undermine the collective trust on which FiDA depends.
The resulting consequences extend beyond technical compromise to legal, financial and strategic harm. Non-compliance with FiDA, DORA or GDPR can trigger regulatory enforcement, civil liability and substantial remediation costs.
Neglecting these defences risks transforming isolated security weaknesses into systemic trust failures, undermining both institutional integrity and the broader success of the FiDA framework.
Final Note
FiDA offers massive transformative potential for Europe enabling personalised financial services, improved competition and consumer empowerment. Yet its success rests on the single pillar of “trust”. If financial institutions and FISPs fail to operationalise continuous verification, secure authorisation and unified directories, the entire ecosystem risks fragmentation and loss of confidence.
Security in FiDA is not a compliance exercise it is a strategic differentiator.
Institutions that lead on trust and resilience will define the next decade of digital finance. In open finance, trust is the foundation and currency; it must be earned, maintained and continuously verified.
As the EEA moves toward an open data economy, data flows more freely across the ecosystem creating attractive targets for fraudsters and unauthorised actors. Third-Party Risk Management is no longer optional. Financial institutions must have absolute clarity over who is accessing their interfaces, whether they are properly authorised, legally permitted to operate in the relevant jurisdiction and are members of the appropriate FDSS schemes.
Without this visibility, unintended data exposure is inevitable, placing customer data, regulatory compliance and institutional reputation at risk. To operate safely and confidently in Open Banking and Open Finance, trust must be constantly verified, never assumed.
If you would like to discuss how Konsentus can help your organisation secure access, reduce third-party risk and operate with confidence in the evolving open finance ecosystem, get in touch.

Brendan Jones
COO, Konsentus